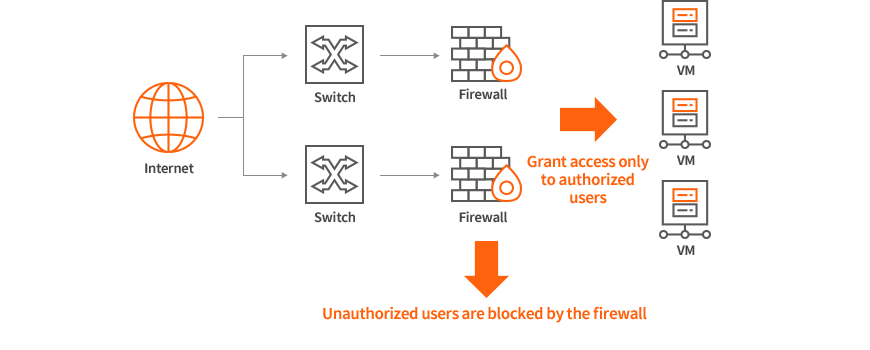
Power Security System for Blocking External Access
Firewall

The AXGATE Firewall is a powerful security system that blocks external access by shutting down all the ports except for the ones that must remain open to provide the necessary services. This prevents network security incidents, blocks external threats or illegal traffic, and allows only normal traffic. Engineers specializing in network security provide 24/7 monitoring and control and protect your services by actively responding to network problems and various adverse situations.
Contact an Expert
Price

| Product | Configuration | HA | Monthly Fee |
|---|---|---|---|
| Standard | Firewall + Monitoring service |
Single | KRW 250,000 |
| Redundancy | KRW 400,000 | ||
| Enterprise | Firewall + IPS + VPN + Monitoring service |
Single | KRW 300,000 |
| Redundancy | KRW 450,000 |
* The monitoring service is provided by one of our partners, GABIA.
How to Use

Sign up
for the service- Sign up for the IXcloud firewall service.
Firewall
installation- KINX’s Operations Team will install a firewall in your project.
Configuration of security settings
- The security and monitoring service provider will contact you to configure the detailed security settings.
Begin
security
/ monitoring services- After the security settings are configured, you will obtain the designated security and monitoring services.
Configuration Diagram

Detailed Features
-
Firewall
· Application of a policy specific to each security zone and log and statistics management
· Implementation of a user-controlled firewall system based on role-based access control policy
· Support policy inspections using virtual packet simulation
· Function for searching for unused security policies and objects
· Provision of statistical information (traffic, session, etc.) on each zone and user -
IPS
· Provision of more than 5,000 signature-based rules
· Detection and blocking of abnormal actions based on signature, protocol, and traffic
· Blocking of snort-based worms, viruses, backdoors, spyware and malware
· Provision of real-time pattern and policy updates
· User defined rule and snort rule format support -
VPN
· Standard IPsec protocol and IKE v1 and v2 support
· Bandwidth-based load balancing
· Line bonding in case of using multiple lines
· Monitoring of traffic loss occurring during transmission and retransmission after receiving the packets in question
· SSL VPN support (OS: Windows, Android, iOS, Linux supported)
Monitoring Service

Even if you have excellent equipment or solutions, you won’t be able to prevent an unforeseen attack without an engineer with professional expertise and skills in this area. KINX can guarantee seamless service 24/7 without any interruptions, with skilled engineers who can actively respond to network issues and various adverse situations.
| Firewall monitoring services |
Detection of external threats using next-generation firewall UTM (IPS, AV) |
|---|---|
| IPS monitoring services |
Prevention of intrusion by inspecting all protocols with the intrusion detection function |
| Event detection and failure response |
Real-time detection of harmful events and traffic and detailed intrusion response analysis |
| Reports/Updates |
Monthly report: Provided once a month (default target: IPS control) |
Recommended to

-

Companies that need to build a powerful security system in line with the latest security technology and trends
-

Companies that need to defend against intrusion through public Internet sessions used by internal/external users
-

Companies that do not have any in-house employees to manage their servers